The decentralized finance (DeFi) world just faced its biggest hack of 2026. On April 1, hackers drained over $270 million from Drift Protocol, a leading perpetuals exchange on Solana. While the timing seemed like an April Fools’ joke, the missing funds are very real.
As the chaos unfolded, Drift Protocol moved to officially confirm what many had already suspected. The team suspended all deposits and withdrawals and said it was working with multiple security firms, bridges, and exchanges to try to contain the damage.
The market also reacted almost instantly. The platform’s native token, DRIFT, dropped sharply, shedding more than 28% within 24 hours. The decline continues, and some reports put the total drop closer to 40%.
The Exploiter’s On-Chain Trail
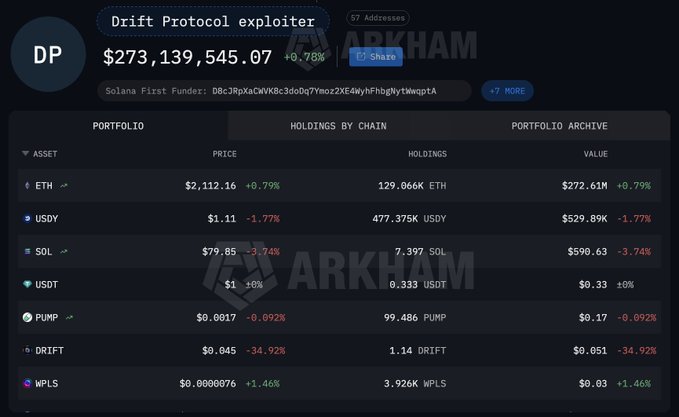
According to Lookonchain’s on-chain tracking, the exploiter started swapping the loot into USDC to purchase Ethereum. The first few transactions were the purchase of 19,913 ETH, worth around $42.6 million at the time. However, that was just the warm-up. By the time it was all over, the attacker had converted the entire stolen pile into roughly 129,066 ETH, valued at approximately $273 million.
Mixin Hacker Spring Back To Action After Two Years Of Inactivity With Ethereum Sale
How The Drift Protocol Hack Happened
Drift Protocol’s own post-incident report shed more light on exactly how this happened. The report reveals that the attacker didn’t just stumble into the protocol. Instead, they spent several weeks preparing, quietly laying the groundwork before pulling the trigger. The key to the whole operation was something called durable nonces—a feature that allows transactions to be pre-signed and executed at a later time. The attacker exploited this to set up delayed transactions in advance so that when the moment came, everything fired off automatically.
On top of that, they managed to compromise multiple multisig signers. The attackers gathered enough approvals to seize control of the administrative body with the highest level of authority over the protocol. Once they had that, the rest was straightforward.
Speaking about the attack, Ledger CTO Charles Guillemet was quick to point out that this had nothing to do with a smart contract flaw. Instead, the multisig that controlled the protocol was what got breached, and possibly well before anyone realized.
His read on it is straightforward. The attackers either obtained enough private keys to clear the multisig threshold on their own. Or, more likely, they quietly compromised the machines of several multisig signers. Guillemet drew a direct line between this attack and last year’s Bybit hack. Both followed the same patient, deliberate playbook. Rather than targeting the code, the attackers went after the humans and the processes behind it. By the time anyone noticed, it was already done.
On the other hand, BitMEX co-founder Arthur Hayes raised a question, showing another view of the situation. He asked if Solana having native multisig addresses built in would have made this attack impossible in the first place. He framed it as genuine curiosity. Still, the implication was hard to miss.
Major Crypto Hacks Cost Investors Over $2.38 Billion in 2025: Details